Emelitere ikpeazụ:
Emelitere ikpeazụ:
 53% of users voted this helpful
53% of users voted this helpful
Transport Layer Security (TLS) certificates verify the integrity of both the ownership and information of websites you visit. This article explains how it works.
Table of Contents
What websites use certificates?
Websites whose addresses start with https use TLS Certificates. Websites using TLS certificates are secure only insofar as they verify two things:
- The website administrator owns the website name or knows who does.
- The website is encrypting the connection between your browser and itself to prevent eavesdropping.
Chain of trust
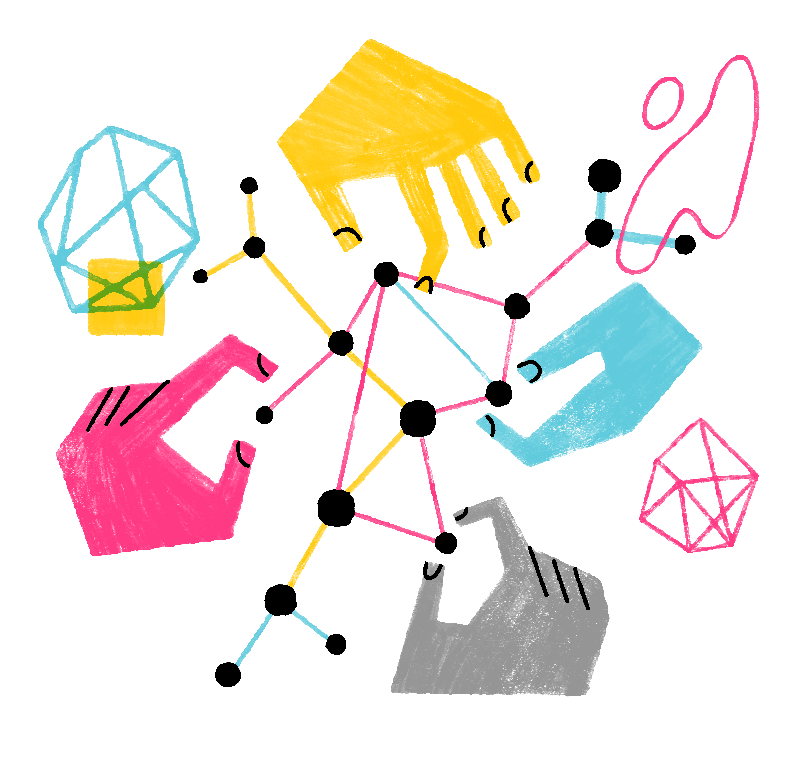
Browsers, such as Firefox, verify certificates through a hierarchy called a chain of trust. It defines a structure for browsers and other programs to verify certificate integrity. This diagram illustrates the chain of trust:
It's a list of three certificates:
- The root (trust anchor) certificate
- The intermediate certificate
- The server (end entity) certificate
Let's define them: the root certificate belongs to the Certificate Authority (CA), which issues TLS certificates and the browser inherently trusts; the intermediate certificate acts as an intermediary between the root CA and the website; the server certificate belongs to the website administrator.
These certificates contain the following information:
- Details about the Certificate Authority (CA)
- An asymmetric key pair:
- A private key that cryptographically signs the next certificate in the chain; the server certificate has one for other tasks.
- A public key for decrypting the signature of the next certificate in the chain for identity verification; the server certificate uses it for other tasks.
Now, we can describe how Firefox determines whether a website is secure.
How does Firefox verify certificate integrity?
Here is how Firefox uses the chain of trust to verify TLS certificates:
- Firefox downloads the certificate of the website you visited.
- Firefox checks the certificate against its internal database of Certificate Authorities (CAs).
- It uses the public key of the root CA certificate to ensure that the root certificate and intermediate certificate properly signed down the chain.
- Firefox checks with the CA to ensure that the website you're connected to match the website on the server certificate.
- Firefox generates a symmetric (single) key for encrypting HTTP traffic for the connection.
- Firefox encrypts the symmetric key with the public key of the server certificate.
- The private key, which is on the web server, decrypts the connection data.
Viewing a certificate
To view a certificate, follow these steps:
- Click on the pad lock icon.
-
- Click on .
-
- Click on .
-
- In the pop-up window, click .
-
Firefox will now open the about:certificate page with the certificate for the website you're on:
The three tabs show, from left to right, the server certificate, the intermediate certificate and the root certificate.
Certificate content
TLS certificates contain the following information:
- Subject: Contains the website name and optional attributes, such as information about the organization owning the certificate.
- Issuer: Identifies the entity that issued the certificate.
- Validity: Shows how long the certificate is valid for.
- Subject Alt Name Extension: Lists the website addresses that the certificate is valid for.
- Public Key Info: Lists attributes of the public key of the certificate.
- Serial Number: Uniquely identifies the certificate.
- Signature Algorithm: Algorithm used to create the Signature.
- Fingerprints: Hash of the certificate file in DER binary format.
- Key-Usage and Extended Key Usage: Specify how people can use the certificate, such as for confirming ownership of a website (Web Server Authentication).
- Subject Key ID: An identifier generated from the TLS certificate's public key as a way to identify the certificate.
- Authority Key ID: An identifier generated from the TLS certificate's public key as a way to identify the public key corresponding to the private key used to sign the certificate.
- CRL Endpoints: The locations of the Certificate Revocation List (CRL) of the issuing CA.
- Authority Info: Contains the validation method for the certificate authority and the intermediate certificate file.
- Certificate Validation: Contains the certificate validation type and a link to the CA's Certification Practice Statement (CPS).
- Embedded SCTs: Lists the Signed Certificate Timestamps (SCTs).
Problematic certificates
When you visit a website whose address starts with https and there is a problem with the TLS certificate, an error page will display. The What do the security warning codes mean? article describes common certificate errors.
To view the problematic certificate, follow these steps:
- On the Your connection is not secure warning page, click
-
- Click on View Certificate.
-
The bad certificate will now display.