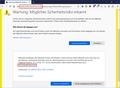
browser warning: potential security risk ahead - ssl_error_bad_cert_domain
the situation: we publish an internal wiki website in our intranet. the delivering server provides a certificate issued by our own microsoft active directory pki (root-intermediate-servercert). firefox is configured by gpos in order to use windows cert store, where root and intermediate are installed. but nevertheless firefox drops an error message ssl_bad_cert_domain and i do not see why. in chrome or chromium based edge everything is fine. no ssl warnings. as you can see in the attached screenshot the cert includes various san fields for different host names, which includes two ip addresses (anonymized).
any advice what do to is mostly appreciated.
thanks a lot peter
この投稿は El Viejo により
選ばれた解決策
indeed, removing the ip addresses from both san fields (dns, ip) did the trick. i do not feel capable to call this a firefox bug but at least it should be brought to the attention of the developers. so i am going to file a bug report (given there is'nt one already).
ps: no need to escalate this as it has been subject of discussion here (and i have learned how to issue certs according the specs :-) so no ip addresses in dns fields). https://bugzilla.mozilla.org/show_bug.cgi?id=1148766
この回答をすべて読む 👍 0すべての返信 (7)
- MOZILLA_PKIX_ERROR_MITM_DETECTED
- uses an invalid security certificate SSL_ERROR_BAD_CERT_DOMAIN
- configured their website improperly
How to troubleshoot the error code "SEC_ERROR_UNKNOWN_ISSUER" on secure websites https://support.mozilla.org/en-US/kb/troubleshoot-SEC_ERROR_UNKNOWN_ISSUER
hello fredmcd, thanks for you quick reply. our ff users get only the ssl_error_bad_cert_domain and it can easily be resolved by setting a security exception but i do not want to do this for known reasons :-) as i mentioned in my first post our pki and the cert are set up the way it is supposed to work. chrome, edge and even good old (or better said bad old) ie do not drop a certificate warning. so my question is: where is the reason why firefox claims a bad domain name in the cert?
i do not want to post the public part of the cert because there is an internal ip address in two fields (dns, ip). could this be the reason for the error message?
I don't know much about such issues and called for more help.
There might be something Firefox doesn't like about the Subject Alt Names field.
For example, a few years ago we had a question where there were IP addresses mixed with regular host names in the field, which perhaps caused Firefox to read it incorrectly. That thread doesn't appear to have been resolved one way or the other:
hello jscher2000, thanks for pointing me to the other thread. i am going to reissue the cert without ip addresses and test it.
選ばれた解決策
indeed, removing the ip addresses from both san fields (dns, ip) did the trick. i do not feel capable to call this a firefox bug but at least it should be brought to the attention of the developers. so i am going to file a bug report (given there is'nt one already).
ps: no need to escalate this as it has been subject of discussion here (and i have learned how to issue certs according the specs :-) so no ip addresses in dns fields). https://bugzilla.mozilla.org/show_bug.cgi?id=1148766
この投稿は El Viejo により
Thank you for reporting back on that. I don't know why browsers disagree on such things.